LEAVE ATTACKERSLEAVE ATTACKERSNOWHERE TO HIDENOWHERE TO HIDE
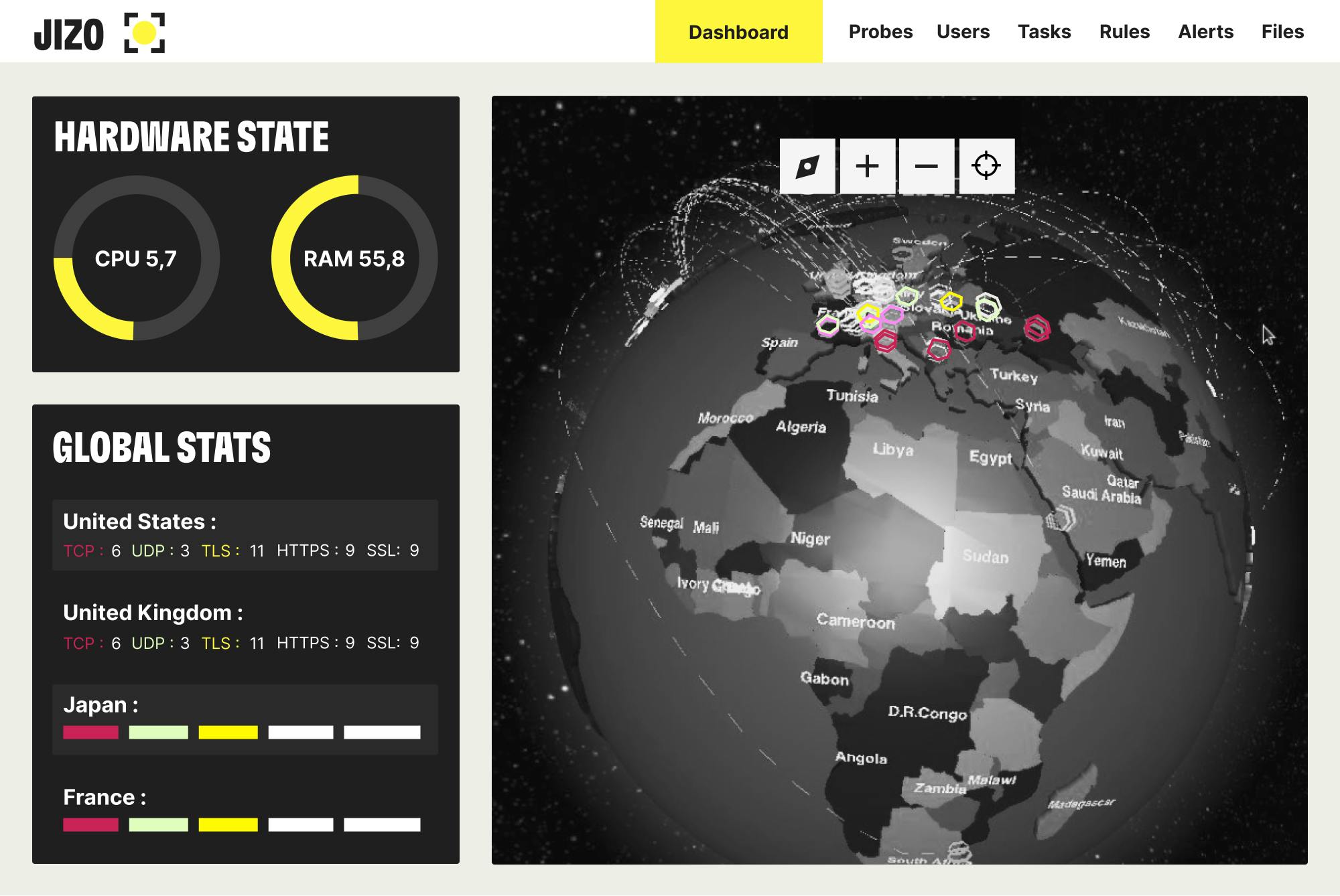
Jizô NDR is the network observability platform that allows decision-makers to anticipate, identify and block cyberattacks.
BEST OF DETECTION WORLDS
Jizô NDR opens up a new generation of network threat detection solutions, by combining the best detection technology, from its traditional signature and malware analysis engines to the most sophisticated AI algorithms and internal Automated Threat Intelligence. Jizô NDR is the best ally of operational cybersecurity and cyber defense teams.
DUAL AI
EMBEDDED IN JIZÔ NDR
Detection amplified with our propietary AI.
GenAI for an absolute understanding of the detected threats, impact and resolution.
EMPOWER
Operational teams finally have the power to implement their own cyber defense strategy.
FIGURES:
Organizations with the most sensitive networks trust Jizô NDR for reliable detection of the most advanced intrusions and threats with no delay.
+100
Jizô NDR deployed
65%
of Sesame it resources dedicated to Jizo NDR R&D
+4 TB
per second of traffic processed by Jizô NDR in 2023 in France
+1 BN
IP packets analyzed per second
MAX. 5%
false positives
2 HOURS
saved every day in the SOC per analyst
HOSHI
Automated Threat Intelligence dedicated to Jizô NDR.

Hoshi delivers daily intelligence to Jizô NDR, updating detection capabilities and allowing for systematic threat contextualization.
Use cases made available to customers give visibility into threats in progress, from the very first stages of compromise, whether threats are targeted, opportunistic or even state-controlled.
The result is significantly accelerated response to attacks.
LOKI
Loki is a threat deception solution. It automatically deploys false resources to divert hackers.

Loki automatically deploy deceptive assets to divert cyber attackers from the network. This allows security teams to better understand hackers and to prepare for new attacks. It has the advantage of not generating false positives. Threat deception, as designed with Loki, significantly optimizes cyber defense capabilities.
