JIZÔ NDR: REVEALS ALL THREATS
Operational teams have an efficient solution for implementing a robust cyber defense strategy.
GET THE BEST OF AI
EMBEDDED IN JIZÔ NDR
DUAL AI TO DETECT ADVANCED THREATS IN YOUR NETWORK
- Detection is amplified with our propietary AI. It serves as the best ally of network protection professionals, who save valuable time for analyzing anomalies and making the right decisions.
- GenAI actively facilitates an absolute understanding of detected threats, their impact, and the strategies for resolution.
SECURE AND SOVEREIGN

JIZÔ NDR RECEIVED THE
QUALIFICATION FROM ANSSI IN 2021
- Sovereign solution
- On-premise with no share of data/ traffic
- Hardened OS for maximum security
- In line with all ANSSI qualification requirements
FLEXIBLE,
FOR SPECIFIC
DETECTION AND USE
Real-time threat detection
in encrypted and unencrypted
network traffic
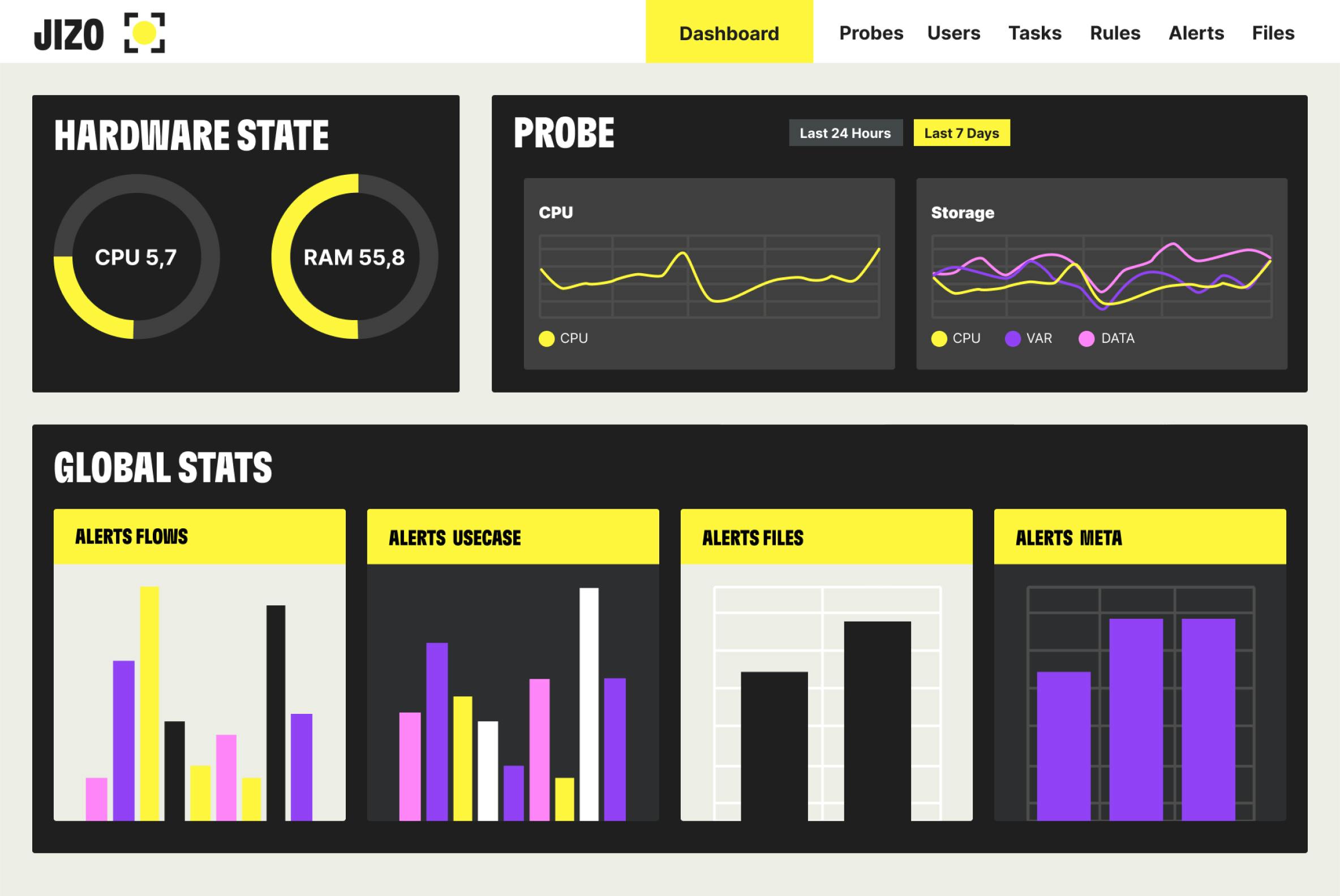
HIGH TRAFFIC PERFORMANCE
- Up to 40 Gbp/s of traffic, and exploitation of thousands of metadata in real time
- Detection even on encrypted traffic
- Full transparency of traffic captured and analyzed, with indication in the event of packet loss
CONTEXTUALIZED DETECTION
FOR DEEPER COVERAGE
COMBINATION OF THE BEST TECHNOLOGIES
FLOW ANALYSIS ENGINE
Real-time detection
with signatures
FILES ANALYSIS ENGINE
Static files signatures, Dynamic
sandboxing, AV
OT DETECTION ENGINE
Real-time mapping
of devices and flows, Dynamic monitoring, pattern & behavioral analysis.
AI ENGINE
Supervised and unsupervised algorithms, network and endpoints behavior analysis.
USE CASES ENGINE
Pre-made or user-created detection sets instantly uncover sophisticated attacks.
DPI & METADATA ENGINE
+4,000 protocols
and applications.
BRING YOUR DETECTION
TO THE NEXT LEVEL
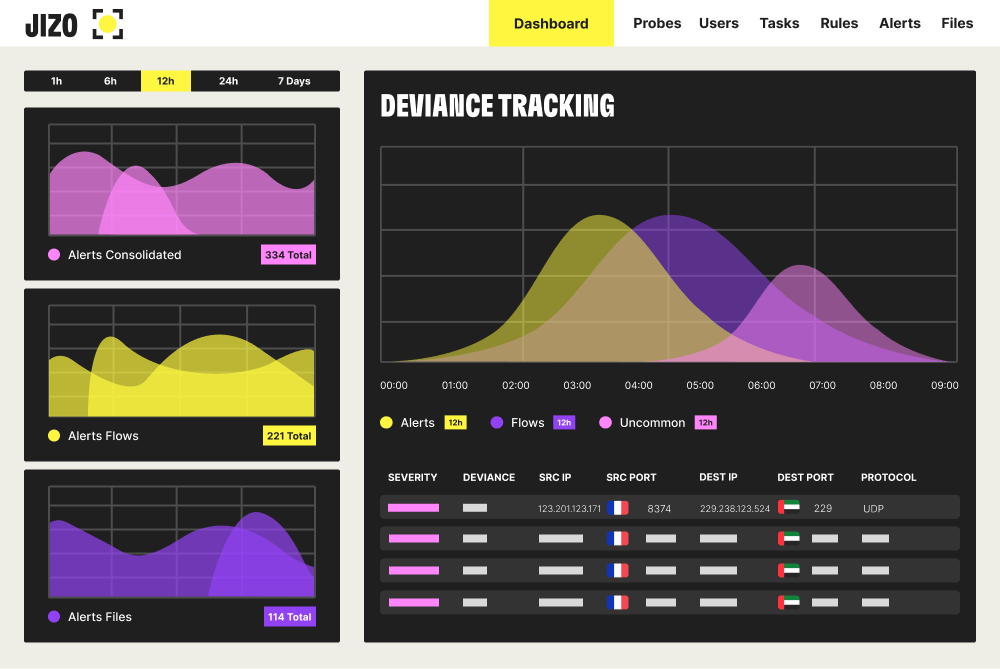
AI-POWERED ALERTS
PROPRIETARY AI TO AUTOMATE,
PREDICT AND REACT FASTER
- Proprietary AI algorithms enrich alerts with context and deviance analysis.
- Advanced triage with integrated risk scoring, correlation, and investigation
- Detection of deviant asset behavior
USE CASES DETECTION ENGINE

UNIQUE FEATURE: A USE-CASE ENGINE DISCOVERS COMPLEX ATTACKS IN ONE CLICK
- Automatically correlated alerts on attack scenarios for contextualization and faster response
AGAINST ADVANCED THREATS, A DEDICATED CTI COVERS SPECIFIC RISKS
BECAUSE YOUR RISK EXPOSURE IS SPECIFIC, YOUR CYBER THREAT DETECTION MUST BE SPECIFIC TOO.
FOCUS ON THE THREATS THAT MATTER TO YOU:
- Adapt detection to particular risks you are exposed to
- Benefit from correlation and deviance analysis capabilities. Technical alerts are translated into business risks.
- Power Jizô NDR with HOSHI detection sets, to deal with the threats that matter.
JIZÔ COMBINED WITH HOSHI:
RISK & THREAT CENTRIC
CTI x NETWORK DETECTION
